The world of Web3 - the so-called 'third generation' of web content which has emerged over the last few years in response to a series of technological developments - continues to generate significant amounts of discussion and speculation. A number of the associated applications present the potential for new types of infringements, brand abuse and online risks, and warrant close attention by brand owners and general Internet users alike.
In this article we consider trends in the Web3 landscape - with a particular focus on blockchain domains - and how these may be driven by external factors, such as developments in artificial intelligence (AI). We also discuss the implications for brand owners and the associated brand protection considerations.
i. Technical definitions
Web3 (a.k.a. 'Web 3.0') is a general term referring to decentralised content on the Internet (i.e. organised on a peer-to-peer basis and without reliance on authoritative hosting providers), with a particular focus on blockchain technologies. The term 'Web3' reflects the emergence of new technologies which provide immersive experiences for users and encourage freedom of speech. It follows on from the definition of Web2 in the early-2000s, to indicate a transition from the 'read-only' days of the early Internet into an ecosystem more dominated by user-generated content.
A blockchain is a publicly accessible digital ledger in which transactions are recorded. It is cryptographically sealed and cannot be modified after its contents are recorded. Blockchains form the basis of many digital currencies (such as Bitcoin), but also have a number of other applications, such as supply-chain control by brand owners. In terms of brand protection considerations, two related concepts are of particular relevance:
- NFTs (non-fungible tokens)[1] - NFTs are cryptographic collectibles comprising any of several types of asset or media. Any digital file can be converted into an NFT through a process known as minting, whereby ownership is recorded on a blockchain. NFTs can take a number of different forms, but are most commonly associated with graphics files (e.g. artworks, branded imagery, etc.) and other types of digital content (such as audio or music files). Brand owners are increasingly incorporating NFTs into their business models, such as the production and trade of virtual branded items (e.g. items to be worn by avatars in virtual-reality environments - part of the 'metaverse', the name given to a generalised connected environment of 3D virtual worlds.
- Blockchain domains - Like regular domains, blockchain domains consist of a second-level domain name and an extension (with specific examples including .eth, .crypto, and .bit), and can be used in a number of different ways, including the construction of decentralised websites (which have special access requirements, such as the use of a dedicated browser like Brave, or a browser plug-in), as memorable wallet addresses for sending and receiving cryptocurrency, or as hosting infrastructure for programs to be run as apps. Blockchain domains are recorded, together with their ownership details, on a blockchain (i.e. are not hosted on a server, or recorded in a regular registry zone file) and, unlike regular domain names, are not governed or regulated by ICANN (the Internet Corporation for Assigned Names and Numbers). They are offered by specialist providers and, although the costs may be higher than for traditional domains, are in many cases offered for registration for a longer period than gTLDs, or involve only a one-off cost to own for ever.
Blockchain domains are attractive to many users because of the inherent security associated with the blockchain infrastructure, and their resistance against traditional blocking or censorship methods. For those with interests in other areas of the Web3 ecosystem, use of blockchain domains may be a natural choice.
Future development of native support of blockchain domains by mainstream web browsers is also likely to significantly drive increased adoption by users. Already, blockchain domain operators are seeking technical workarounds to drive the interoperability of blockchain domains with regular browsers. One example is eth.link, a service allowing .eth blockchain domains to be accessed via DNS, by appending '.link' to the blockchain domain name[2].
ii. Brand protection implications
From a brand monitoring point of view, blockchain domains are generally difficult to identify, both because of the absence of zone files (which, for regular domains, provide comprehensive lists of registered domains across the individual domain extensions, or TLDs (top-level domains)), and because of the specific website access requirements. One commonly-used technique to circumvent this difficulty can be to search for references to the blockchain domain names being traded in NFT marketplaces (for example, where the current owner can offer the sale of a domain to another interested party, which may be a brand owner or a would-be infringer), and some blockchain domain providers also provide searchable databases of registered domains. However, more robust methods are likely to require direct monitoring of the content of the blockchains themselves, or searches across databases of transactions which have occurred on a specific blockchain.
Enforcement options are also currently limited, with one option being just to take down infringing listings offering the sale of a blockchain domain from the Web3 marketplace - although this does not deactivate the domain name itself or change its ownership. Some blockchain domain providers are becoming more mindful of the risks posed by cybersquatters[3], and offer brand owners the ability to block third-party registrations (similar to the Trademark Clearinghouse (TMCH) programme for new gTLDs) or to claim ownership of trademarked names. However, these blocks are at the discretion of the domain providers, making them subject to change and in need of periodic monitoring.
Additionally, wallet addresses associated with specific blockchain domain or NFT owners - as might be available through public records, Web3 marketplaces, or blockchain domain providers - can be used as the basis of an investigation to identify additional associated information relating to the entity in question. In some cases, it may also be possible to submit a court order to the service provider for the disclosure of collected data.
As a further brand protection initiative, brand owners may also wish to consider proactively defensively registering key domain name keyword strings across relevant extensions. This approach is generally more cost-effective than attempting to subsequently acquire domain names of interest.
The changing landscape
A number of recent factors - primarily driven by developments in AI technologies - may very well impact on the role of Web3 within the wider Internet landscape, even if (as we shall see) we have not yet seen any major new growth in the level of uptake of the relevant technologies.
The developers of AI products and services such as ChatGPT are increasingly using the data held by platforms such as Reddit and Twitter as an input for their training models, resulting in the introduction of initiatives by these platforms to prevent or monetise this activity. In April 2023, Reddit announced plans to start charging for use of its data API[4], resulting in a number of subreddits (communities) - or associated applications - being made private, or shutting down altogether[5], ('going dark') in protest[6,7]. In July, Twitter introduced a measure to limit the number of posts a user could read per day[8], to prevent "extreme levels of data scraping and system manipulation"[9]. The actions taken by online platforms to remove and restrict access to content are widely seen as being contrary to a fundamental characteristic of Web2, namely the ability of individual users to create and curate their own content, and choose which content to consume from other users.
It is interesting to note that Web3 and the metaverse has recently been declared 'dead' by some commentators[10], following moves by Meta and Mark Zuckerberg - together with other industry leaders - away from these areas, in favour of development of generative AI[11]. However, it is perhaps that very trend - and the associated reactions by service providers - which may point us back to the need for a Web3, being inherently decentralised and less prone to regulation and restriction. Could these technologies see a new lease of life as a safe harbour for the community-owned content which used to be the province of Web2[12]? The answer is a resounding 'yes', according to AI commentator Alex Valaitis, who recently tweeted that "AI becomes stronger the more centralized it gets, which is exactly why we need Web3 as a counterweight[;] think of public blockchains as the last bastion of the open internet"[13].
The existence of the Web3 Domain Alliance[14] is also noteworthy. It features many of the major Web3 service providers as members, and is intended to drive "consumer protection, preventing naming collisions, fair and open use of intellectual property in the industry, and interoperability of blockchain naming systems"[15]. As part of this initiative, Unstoppable Domains announced in February 2023 that it would not enforce a key patent - relating to the use of smart contracts[16] in the blockchain domain naming process - against other members of the group[17].
The Web3 ecosystem also presents its own problems, however, such as the ongoing US litigation between Unstoppable Domains and Wallet Inc. over rights to offer domains across the .wallet extension[18].
Observed trends in blockchain domains and Web3 content
There is evidence of a significant amount of (at the very least, legacy) interest in Web3 concepts; searches across the (gTLD) zone files provided by ICANN show that, as of July 2023, there are over 300,000 registered (regular) domain names containing the Web3-related keywords 'web3', 'nft', 'blockchain' or 'metaverse'.
Currently, there are around 7 million blockchain domains registered, with two of the most popular providers - Ethereum Name Service ('ENS') (which offers .eth domains on the blockchain associated with the Ethereum cryptocurrency) and Unstoppable Domains (offering blockchain domains across a range of more than ten extensions) - having provided 2.7 million[19] and 3.6 million[20] registrations, respectively.
In the remainder of this article, we consider activity surrounding .eth registrations as a proxy for the overall blockchain domain landscape, both because of the popularity of the Ethereum Name Service and because of the ready availability of associated statistics available through information and tools provided by Dune Analytics.
Dune states that, as of 17 July 2023, there are 2,719,569 active ENS (.eth) blockchain domains[21]. The registration history of these domains is available back to May 2019, and is shown in Figure 1.

Figure 1: Monthly numbers of .eth blockchain domain registrations
The statistics show a very large peak in activity covering roughly the calendar year of 2022, after which levels of registrations appear to have dropped off for now. This is consistent with the flurry of activity where available three- and four-digit domains were being rapidly registered, with the monthly trading volume peaking at $44.3 million in May 2022[22].
It is also possible to extract more granular data, looking at the individual blockchain domain registrations (names and registration dates), for the last year (July 2022 – July 2023)[23] (Figure 2).

Figure 2: Daily numbers of .eth blockchain domain registrations (July 2022 – July 2023)
Within this dataset of 1.47 million blockchain domains, we consider the prevalence of domains with names containing each of the top ten most valuable global brands in 2023 (according to data provided in the latest Kantar BrandZ study[24]). This dataset (see Table 1 and Figure 3) provides a measure of the likely level of potential brand infringement across the blockchain domain landscape.
Brand string
|
No. registered .eth domains
(July 2022 - July 2023)
|
| apple |
902 |
| google |
625 |
| microsoft |
249 |
| amazon |
926 |
| mcdonalds |
136 |
| visa |
301 |
| tencent |
43 |
| vuitton |
119 |
| mastercard |
66 |
| coca(-)cola * |
160 |
* The hyphen in the brand string is optional, so the data considers examples containing 'cocacola' or 'coca-cola'.
Table 1: Total numbers of .eth blockchain domains registered between July 2022 and July 2023 with names containing each of the top ten most valuable global brands in 2023

Figure 3: Monthly numbers of .eth blockchain domain registrations with names containing each of the top ten most valuable global brands in 2023
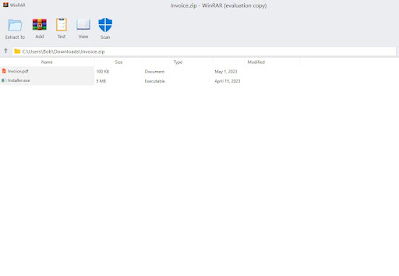
It is also worth noting that the inclusion of Unicode support in the blockchain domain infrastructure allows special characters such as emojis to be included in the domain names[25]. Consequently, the dataset includes examples such as those shown in Figure 4, many of which have the potential to be used to create highly deceptive and/or purportedly official websites.

Figure 4: Examples of branded .eth blockchain domain names with names including special characters
A similar previous study published on the DNS Research Federation blog has highlighted the potential for such domains to be used fraudulently or for other infringing purposes, and identified multiple instances of prolific serial registrants, each in ownership of over 100 branded domain names[26]. The difficulties with monitoring and enforcement across the blockchain landscape also makes these domains attractive to cybersquatters[27].
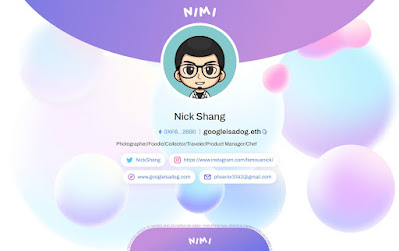
Currently, very few of the branded blockchain domains in the dataset resolves to any significant content, although a small number of live sites or active website responses were identified (Figure 5). These include one webpage (Figure 5(iii)) analogous to a server index page, which is sometimes seen with sites under development as a precursor to subsequent, more significant website content, or when 'hidden' (potentially harmful) content is present in one of the subdirectories.
(i)
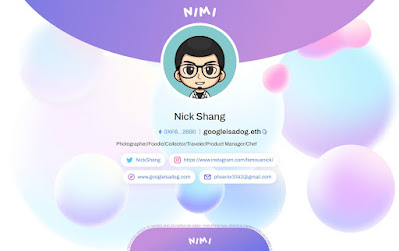
(ii)

(iii)

(iv)
Figure 5: Examples of live websites or other active webpage responses associated with .eth blockchain domains with names containing any of the top ten most valuable global brands in 2023 - (i) googleisadog.eth; (ii) whalevisa.eth (potentially unrelated to the Visa brand); (iii) tencentglobal.eth; (iv) googlenoodle.eth
Conclusions
These observations raise a number of questions about the likely direction of Web3 trends going forward. Arguably, there is a case to be made that the peak in activity in blockchain domain registrations took place in 2022, and has now greatly subsided. However, it may simply be that this time period simply represented a 'golden age' for registrations, when significant numbers of the highly-desirable available domain names were snapped up by prospectors; the creation of a pre-existing landscape to which future activity will be added. It is also possible that the nascent nature of Web3, and uncertainty by brand owners over which department should take responsibility for blockchain domains, has resulted in reluctance by corporations to embrace and adopt the technologies.
Furthermore, there must also be questions surrounding the use of an analysis of domains with just a single extension, on a single blockchain, as a proxy for the whole Web3 ecosystem.
Overall, however, it seems reasonable to assert that AI technologies - and other technological and societal developments - may well drive a resurgence of interest in Web 3. Given the scale of legacy activity in the associated areas, and the numbers and nature of associated infringements, it seems advisable for brand owners to be mindful of blockchain domains targeting their brands, and to carefully consider their own brand-protection strategies in the Web3 arena.
References
[1] https://www.linkedin.com/pulse/rise-nft-david-barnett
[2] https://eth.link/
[3] https://www.brandsec.com.au/blockchain-domains-and-cybersquatting/
[4] https://techcrunch.com/2023/04/18/reddit-will-begin-charging-for-access-to-its-api/
[5] https://www.reddit.com/r/apolloapp/comments/144f6xm/apollo_will_close_down_on_june_30th_reddits/
[6] https://news.sky.com/story/reddit-blackout-thousands-of-communities-are-doing-dark-today-heres-why-12899280
[7] https://www.theverge.com/2023/6/30/23779519/reddit-third-party-app-shut-down-apollo-sync-baconreader-api-protest
[8] https://www.bbc.co.uk/news/technology-66093324
[9] https://twitter.com/elonmusk/status/1675187969420828672
[10] https://www.splunk.com/en_us/blog/learn/blockchain-web3-dead.html
[11] https://www.businessinsider.com/metaverse-dead-obituary-facebook-mark-zuckerberg-tech-fad-ai-chatgpt-2023-5
[12] https://cointelegraph.com/news/how-adoption-of-a-decentralized-internet-can-improve-digital-ownership
[13] https://twitter.com/alex_valaitis/status/1674840503861248018
[14] https://www.web3domainalliance.com/
[15] https://cointelegraph.com/news/web3-domain-alliance-expands-with-51-new-members
[16] https://www.investopedia.com/terms/s/smart-contracts.asp
[17] https://fortune.com/crypto/2023/02/22/unstoppable-pledges-patent-non-aggression-pact-across-expanded-web3-domain-alliance/
[18] Unstoppable Domains, Inc. v. Wallet Inc. et al. 1:2022cv01231
[19] https://ens.domains/
[20] https://unstoppabledomains.com/
[21] https://dune.com/makoto/ens
[22] https://dappradar.com/blog/best-blockchain-web3-domain-names-services
[23] https://dune.com/makoto/ens-released-to-be-released-names
[24] https://www.kantar.com/inspiration/brands/revealed-the-worlds-most-valuable-brands-of-2023
[25] https://nptacek.medium.com/experimenting-with-ens-c88bfe7ed246
[26] https://dnsrf.org/blog/brand-names-in-blockchain-domains---new-frontier-for-brand-owners/index.html
[27] https://www.thefashionlaw.com/the-rise-in-blockchain-domains-presents-risks-opportunities-for-brands/
This article was first published on 26 July 2023 at:
https://www.iamstobbs.com/opinion/trends-in-web3-part-1-a-look-at-blockchain-domains